IT
The Risks of Shadow IT and How to Avoid Them
By Gilad Maayan •
This brief guide introduces you to Shadow IT, explains some of the common risks involved, and offers advice on how you may mitigate them. What Is Shadow IT? Shadow IT is an IT system or technology used without the knowledge or approval of an organization. This can include personal devices like cell phones and USB…
Read More Back to School Solutions, Optimizations, and More: August Blog Roundup
By Ruby Brown •
Summer is coming to a close, so before the fall hits full swing it’s a good time to catch up. This is our list of the top 5 blogs we published this month. 1) SiteSpect Synopsis: All About Influencer Marketing Influencer marketing keeps growing, but not in the way that we expected. Read what experts…
Read More The Ferris Wheel of IT Troubleshooting
By SiteSpect IT •
If you’re in IT, you’ve probably encountered a situation like this: A key component of your application stopped working. Your offshore development team assures you that it is not the code base. So, you call your CDN provider and ask them to investigate. They don’t see anything wrong and suggest you look further upstream. You…
Read More Bad Bots and How to Stop Them
By SiteSpect IT •
Everyone knows that bots can be really bad news. Did you know that today automated bots outnumber humans on the internet? As a result, they are often mistaken for real users. The marketing team wants their activity filtered in order to get quality metrics, which means IT gets the headache of resolving these issues as…
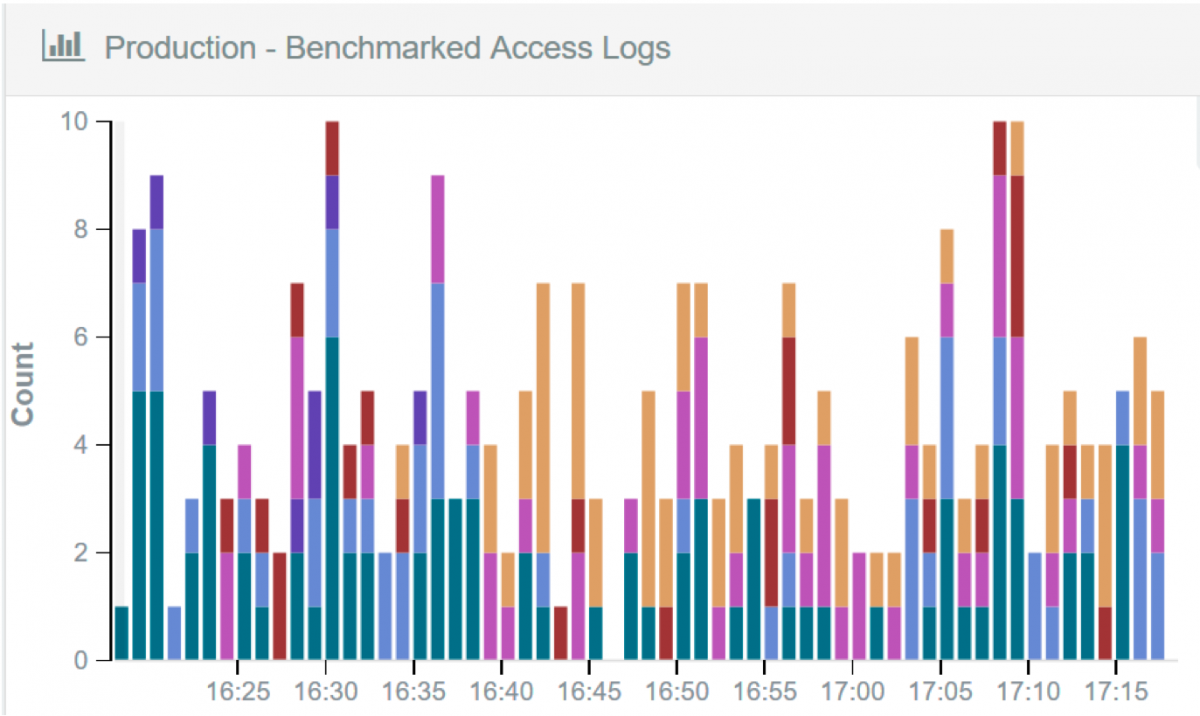
Read More How to Diagnose, Solve, and Prevent Traffic Problems… With an A/B Testing Solution?
By SiteSpect IT •
Your RUM based monitoring system just fired off an alert for latency. Your system logs do not reveal anything out of the ordinary, but your site is slowing down. Where do you go from here? When your site begins to underperform or exhibit an increase in errors, you run the risk of conversions decreasing. Finding…
Read More - « Previous
- 1
- 2
Subscribe to our blog: